1. Solved: Stats by hour - Splunk Community
Solved: I would like to create a table of count metrics based on hour of the day. So average hits at 1AM, 2AM, etc. stats min by date_hour, avg by.
I would like to create a table of count metrics based on hour of the day. So average hits at 1AM, 2AM, etc. stats min by date_hour, avg by date_hour, max by date_hour I can not figure out why this does not work. Here is the matrix I am trying to return. Assume 30 days of log data so 30 samples per e...
2. How to get stats by hour and calculate percentage - Splunk Community
1 mrt 2022 · Solved: Hi There, I am trying to get the an hourly stats for each status code and get the percentage for each hour per status.
Hi There, I am trying to get the an hourly stats for each status code and get the percentage for each hour per status. Not sure how to get it.my search | | bucket _time span=1h | stats count by _time http_status_code | eventstats sum(count) as totalCount | eval percentage=round((count/totalCount),3...
3. How to search the count and average count of events per hour?
14 aug 2015 · Solved: Hello Please can you provide a search for getting the number of events per hour and average count per hour?
Hello Please can you provide a search for getting the number of events per hour and average count per hour?
4. How to search for Count by day by hour or half hou...
Solved: I need to get count of events by day by hour or half-hour using a field in splunk log which is a string whose value is date - e.g..
I need to get count of events by day by hour or half-hour using a field in splunk log which is a string whose value is date - e.g. eventPublishTime: 2022-05-05T02:20:40.994Z I tried some variations of below query, but it doesn't work. How should I formulate my query?index=our-applications env=prod...
5. Solved: Data visualization over the day (by hours) - Splunk Community
24 aug 2020 · Solved: Hi there, I know it sound pretty easy, but I am stuck with a dashboard which splits the events by hours of the day, ...
Hi there, I know it sound pretty easy, but I am stuck with a dashboard which splits the events by hours of the day, to see for example the amount of events on every hours (from 00h to 23h) My request is like that: index=_internal | convert timeformat="%H" ctime(_time) AS Hour | stats count by Hour |...
6. Solved: group search results by hour of day - Splunk Community
13 apr 2021 · I want a chart that tells me how many counts i got over the last 7 days grouped by the hour of the day for a specific user and status number.
Hi splunk community, I feel like this is a very basic question but I couldn't get it to work. I want to search my index for the last 7 days and want to group my results by hour of the day. So the result should be a column chart with 24 columns. So for example my search looks like this:index=myIndex...
7. How to write Stats count by hourly trend list? - Splunk Community
10 apr 2022 · I want count events for each hour so i need the show hourly trend in table view. Regards.
Hello dears, Can i list search result with stat count like hourly trend ? Example; Hour : 00:00 EventCount: 10 Hour : 01:00 EventCount: 15 Hour : 02:00 EventCount: 23 . . Hour : 23:00 EventCount : 127 Regards.
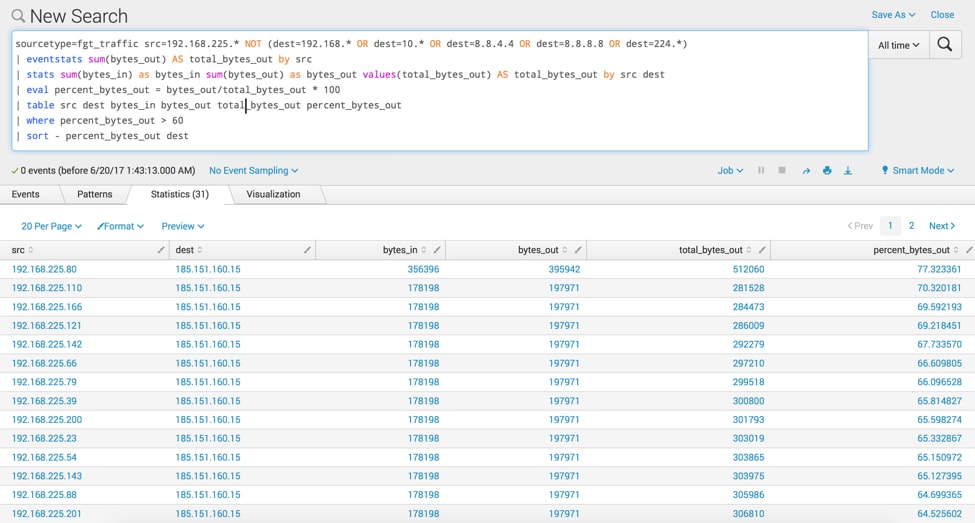
8. Using the timechart Command - Kinney Group
20 jun 2024 · This command will generate a time chart showing the count of events in the _internal index over the default time span. Selecting the Line Chart ...
Explore the functionalities and usage of Splunk's timechart command to create visual representations of time-based data.
9. Stats per hour? - Splunk Community
12 feb 2016 · Instead, I only get a total count for the whole query time period (24hrs in this case), and a listing of users with count>3 for those 24 hrs.
So, I was looking at this: https://answers.splunk.com/answers/205556/how-to-set-up-an-alert-if-the-same-error-occurs-mo.html Started with that to set up a report showing number of users with more than nnnn events per hour. I though this query would give me per hour stats, for users with more than 3 ...
10. Average Splunk Web requests by hour - - GoSplunk
... date_hour=mvrange(0,24,1) | eval count=0 | mvexpand date_hour ] | stats sum(count) as count by date_hour _time | stats avg(count) as avg by date_hour | sort ...
This query is pretty awesome! It helped enlighten us to exactly when our splunk infrastructure is being hit with users index=_internal sourcetype=splunk_web_access [ rest / splunk_server=local | fields splunk_server | rename splunk_server as host ] | bin _time span=1d | stats count by date_hour _time | appendpipe [ fields _time | dedup _time | eval […]
11. How to find an Average Count over an hour in 5 min... - Splunk Community
10 apr 2019 · )_" | bin span=5m _time | stats count by _time instance | stats avg(count) as Average by instance. If you require those zeros provided by the ...
Hi Experts! So I have an issue with GC cycles and we have this logged in splunk. I have used the below query which gives me the minor occurrences count overall (and works fine ) sourcetype=system*process*gc* "[GC pause" | rex field=source "print.prod..?(?.?)\/" | rex field=source "system_print(?.*?)...
12. Splunk stats count by hour - modvolf
21 mei 2024 · splunk stats count by hour. “Our product provides visibility into what is happening, which can enable early detection.” splunk stats count by ...
“Our product provides visibility into what is happening, which can enable early detection.”
13. Using 'group by' For Multiple Fields in Splunk - OpenObserve
5 mei 2024 · index=web_logs status=200 | stats count by hour, page. With this query, Splunk will group the data by both the hour and the page visited ...
See AlsoCnas Breadth RequirementsUnlock advanced data insights in Splunk with 'group by' for multiple fields.
14. Calculating events per slice of time - Implementing Splunk (Update)
Calculating average events per minute, per hour shows another way of dealing with this behavior. ... stats count by _time. The bucket command rounds... Previous ...
Implementing Splunk Second Edition
15. Getting Average Number of Requests Per Hour - Splunk Community
So, this search should display some useful columns for finding web related stats. ... Yes, but if I increase the span to 1d shouldn't I then get the average count ...
I've read most (if not all) of the questions/answers related to getting an average count of hits per hour. I've experimented with some of the queries posted by fellow splunkers and for the most part they've worked when using small queries (i.e. charting the two fields Total Count and Average Count ....
16. Comparing Stats Time Over Time - - GoSplunk
Vote Up +6. Vote Down -0. You already voted! index=_internal earliest=-48h latest=-24h | bin _time span=10m | stats count ... Splunk License Consumption via ...
index=_internal earliest=-48h latest=-24h | bin _time span=10m | stats count by _time | eval window="yesterday" | append [ search index=_internal earliest=-24h | bin _time span=10m | stats count by _time| eval window="today" | eval _time=(_time-(60*60*24))] | timechart span=10m sum(count) by window This search will lay a count of something (in this case, just a count) […]
17. How to create a chart to show count of events by hour over days in a week?
27 jun 2018 · index=_internal | timechart count BY sourcetype | table _time splunk* mongo* * ... | stats count as hourcount by hour | bin hour as day span=1d | ...
Below is the search query i used in order to get a similar chart but the hours are not consecutive, as shown in the Legend's table on the right side. What i have in mind was to create a chart that displays the count of high severity events by hour in a day for a week and have the chart start on a Mo...
18. Count of events from yesterday and today - Splunk Searches
... hours and another showing the number of events ingested in the previous 24 hour period ... stats count by _time | eval window="Yesterday" | append [search index ...
This Splunk search will provide a timechart that shows two series, one demonstrating the number of events ingested in the most recent 24 hours and another showing the number of events ingested in the previous 24 hour period. The results of this search are best viewed as a line chart and will allow you to compare data ingest of today compared with yesterday.
19. Line graph: Count per hour with a trendline that p... - Splunk Community
Line graph: Count per hour with a trendline that plots the average count every 24 hours. ... | stats count as "Transactions" by epochTime | convert ctime( ...
I have a line graph that displays the number of transactions per hour. I want a trendline to go with it, but I want it to give me the average transactions every 24 hours. I have to use epochTime because I'm using the client's timestamp instead of Splunk's _time. In other words, the query works excep...
20. Is there a way to display Count per hr for last 24... - Splunk Community
eval date_hour = strftime(_time, "%H") | stats avg(count) as average by date_hour | eval average = round(average) | fields date_hour average ] | fields - ...
Hi Splunk Gurus, Hoping someone out there might be able to provide some assistance with this one. I have a requirement to be able to display a count of sales per hr for the last 24 hrs (with flexibility to adjust that as needed), but also to show the average sales per hr for the last 30 days as an o...
21. Use Splunk to count DNS queries by hour - Jason Murray
10 sep 2020 · ... hour . It then sorts and counts the dates to get hourly stats. splunk. 84 Words. 2020-09-10 16:34 -0500. Newer FQDN DNS updates using DHCP ...
Splunk search string to count DNS queries logged from Zeek by hour: index="prod_infosec_zeek" source = /logs/zeek/current/dns.log NOT rcode_name = NXDOMAIN | eval c_time=strftime(ts,"%m/%d/%y %H") | table c_time | stats count by c_time Splunk results: c_time count ... 09/10/20 12 8563941 09/10/20 13 27413725 09/10/20 14 33185289 09/10/20 15 30942267 09/10/20 16 22590486 09/10/20 17 3876147 ... The query works by converting the EPOCH timestamp Zeek creates into the human readable format: month/day/year hour.
22. Splunk - Stats Command - Tutorials Point
Splunk - Stats Command - The stats command is used to calculate summary statistics on the results of a search or the events retrieved from an index.
Splunk - Stats Command - The stats command is used to calculate summary statistics on the results of a search or the events retrieved from an index. The stats command works on the search results as a whole and returns only the fields that you specify.

23. timeChart() | Data Analysis 1.143.0-1.147.0
timeChart() · Show the number of events per hour over the last 24 hours. · Instead of counting all events together, you can also count different kinds of events.
Falcon LogScale Documentation
24. Report hourly max count events per day over a month - Splunk Community
I think I m missing something on splunk reporting concepts: | timechart span=1h count as HourlyCount | timechart span=1d max(HourlyCount); | stats count AS hit ...
Hello, I m trying to get the hour per day which gets the most hits on my application over a month but having some issues to get the right data output. I would like to get a table report which would have: DAY1 HOURX MaxEventNumber DAY2 HOURX MaxEventNumber .... I tried the following queries but none ...